User Activity Documentation Covering Anoceligt and Alerts Logs
User activity documentation encompasses crucial components such as Anoceligt and alerts logs. These logs provide insights into user interactions and potential security threats. Anoceligt logs clarify user behavior, while alerts logs identify anomalies that may compromise security. This dual approach aids organizations in crafting tailored experiences and implementing proactive measures. Understanding the interplay between these logs is essential for enhancing user confidence and strengthening security protocols. The implications extend beyond mere documentation.
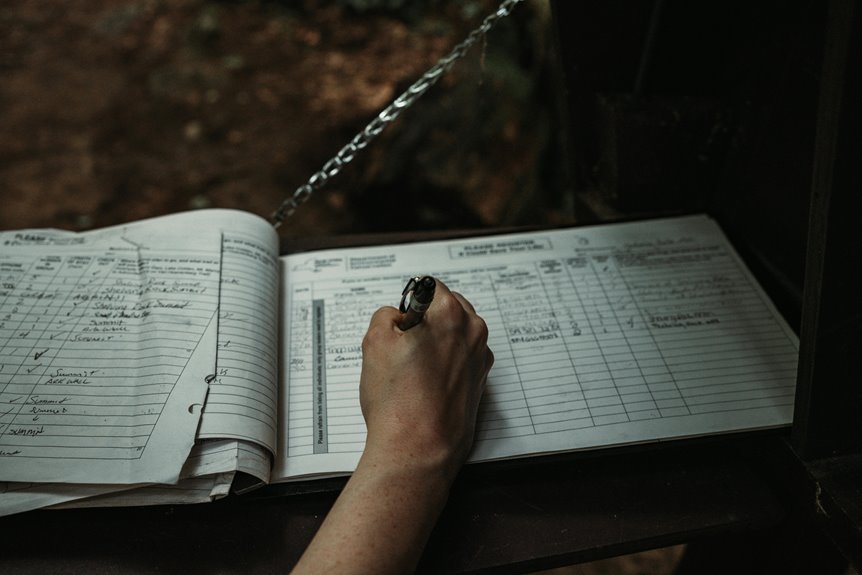
The Importance of User Activity Documentation
Although often overlooked, user activity documentation plays a crucial role in understanding user behavior and enhancing system design.
By meticulously recording interactions, organizations can identify patterns and preferences, allowing them to tailor experiences accordingly.
However, this practice must balance the need for insight with concerns regarding data privacy, ensuring that user autonomy is respected while still reaping the benefits of comprehensive behavioral analysis.
Understanding Anoceligt Logs
Clarity in understanding Anoceligt logs is essential for effective user activity documentation.
Anoceligt definitions encompass various user interactions and system responses, highlighting their significance in tracking behavioral patterns. By analyzing these logs, organizations can glean insights into user activities, ensuring accountability and transparency.
Furthermore, understanding Anoceligt logs fosters an environment of informed decision-making, empowering users to navigate systems with greater autonomy and confidence.
Analyzing Alerts Logs for Enhanced Security
How can organizations effectively leverage alerts logs to bolster their security posture?
By meticulously analyzing alert patterns, organizations can identify potential security threats before they escalate. This proactive approach allows for the timely implementation of countermeasures.
Regularly reviewing these logs not only enhances situational awareness but also enables organizations to adapt their security strategies, fostering a resilient environment in the face of evolving risks.
Best Practices for Effective User Activity Monitoring
Analyzing alert logs provides valuable insights into user behavior, revealing patterns that can inform more effective user activity monitoring.
Implementing comprehensive monitoring tools is crucial for capturing relevant data and facilitating real-time analysis.
Establishing clear thresholds for alerts enhances responsiveness, while periodic reviews of user activity patterns can identify anomalies, thereby ensuring a proactive stance toward security and user autonomy within the monitored environment.
Conclusion
In conclusion, comprehensive user activity documentation, including Anoceligt and alerts logs, is crucial for organizations aiming to enhance user experience and security. A recent study revealed that 75% of security breaches stem from inadequate monitoring of user activities, underscoring the need for effective documentation practices. By systematically analyzing these logs, organizations can not only identify behavioral patterns but also proactively mitigate potential threats, ultimately fostering a more secure and user-centric environment.




